Author

Kemi Olunloyo
Share



It's a scenario every managed service provider has lived through at least once.
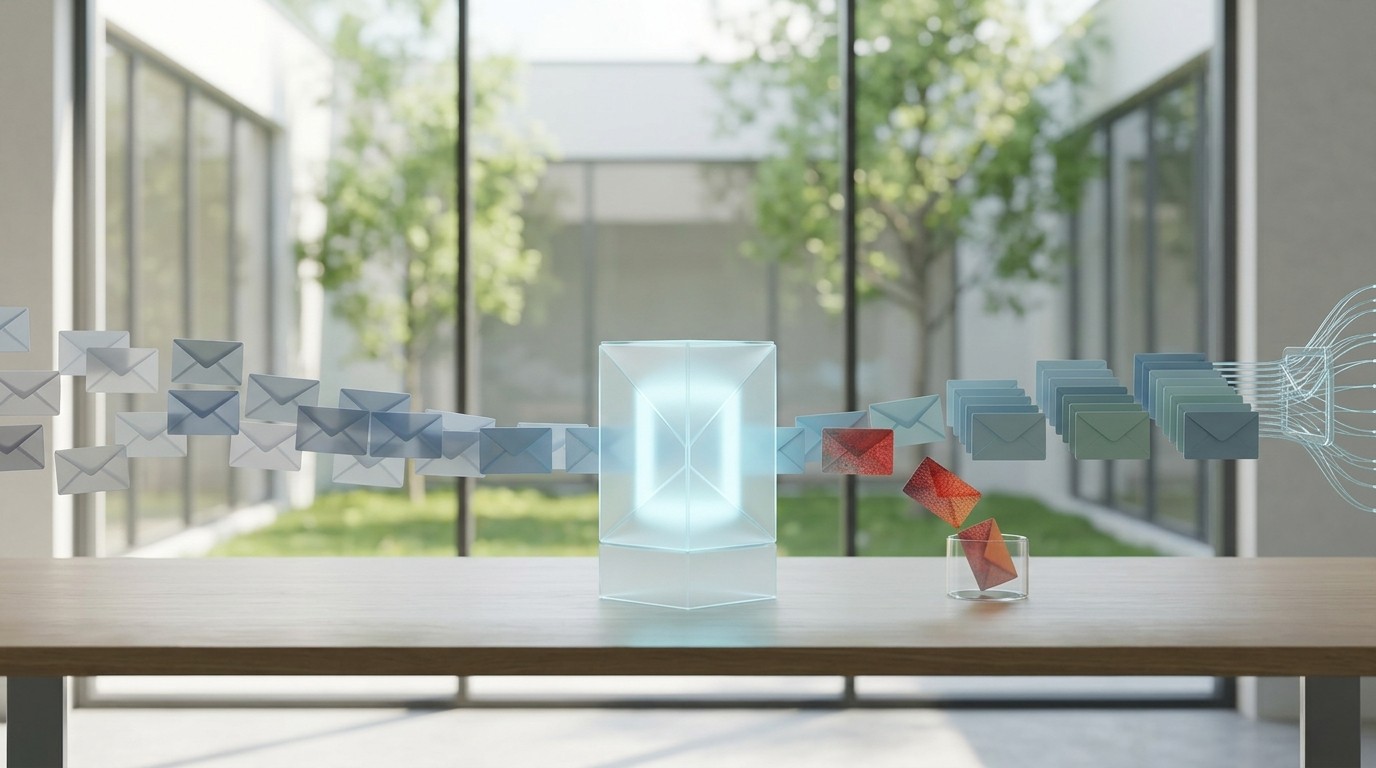
A client receives a phishing email. They recognize something is off; suspicious sender, a strange link, urgent language. So they do what feels responsible: they forward it to the entire company with a warning. "Watch out for this one."
Every single employee. All at once.
What started as one threat vector instantly becomes dozens. Inboxes flood. Links get clicked out of curiosity. Credential harvesting pages load across the building. A contained phishing incident becomes a company-wide security emergency, not because of a sophisticated cyber attack, but because of a well-meaning employee who didn't know the right process.
For MSPs and IT support teams, this isn't a horror story. It's a Tuesday.
So why does it keep happening?
The answer isn't a lack of security awareness training. Most organizations have had the conversation: "Don't click suspicious links. Report phishing emails to IT." Employees know the rule. What they don't have is a clear, frictionless way to act on it.
Ask any MSP technician, and they'll share their own version: the client who CC'd a phishing link directly into a support ticket. The user who printed the suspicious email and posted it on the break room bulletin board, URL fully visible. The employee who pasted the link into a company-wide chat to "warn everyone."
The situations differ. The root cause never does.
Humans under pressure, without a simple and obvious reporting path, will improvise. And in cybersecurity, improvisation is dangerous.
The gap isn't between employees who care and employees who don't. It's between intent and process, and it's costing MSPs more than most realize.
In Part 2, we break down exactly what happens inside your IT support operation when a phishing incident like this lands - and where MSP margins quietly disappear in the chaos.
→ Read Part 2: The Hidden Operational Cost of Every Phishing Incident





